Methodology: stalk, wait, strike, hold
The four-phase Mantis methodology mirrors how a real praying mantis hunts: motionless stalk, patient calculus, instantaneous strike, quiet grip on the catch.
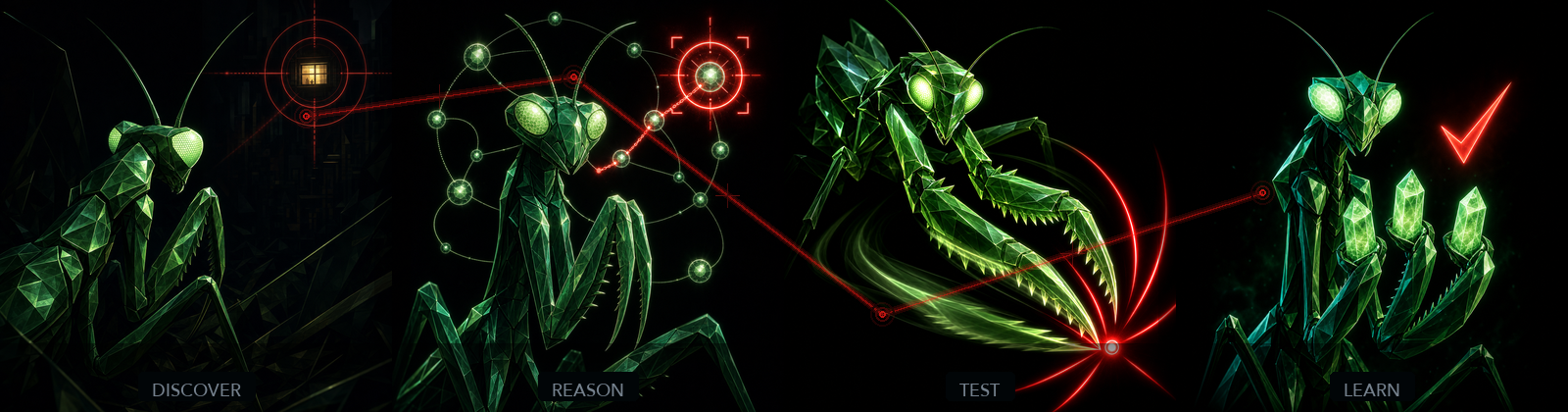
DISCOVER · Stalk
Map the surface before you touch it. The mantis is invisible until the prey is in range.
Implemented by RECON + AUTH.
- Subdomain enumeration (
subfinder) - Live-host probing (
httpx) - Archived-URL crawl (Wayback / OTX / crt.sh)
- Tech fingerprinting from response headers + body
- Nuclei templates for known-CVE coverage
- JS endpoint extraction
- 4-tier signup flow: API POST → browser auto-signup → assisted manual → token paste
Output: attack_surface.json grouped by priority, plus auth.json with attacker + victim profiles when available.
REASON · Wait
Pick the strike-path before the forelegs move. Vendor-aware bypass selection, kill-chain hypotheses.
Implemented by the planning portion of HUNT + CHAIN.
The hunter agent, on spawn, calls mantis_read_hunter_brief and receives:
- Its assigned surface (one per agent, never more)
- The vendor-aware bypass table matched to the surface's
tech_stack+ edge vendor - Exclusions filtered to its surface (dead ends, WAF-blocked endpoints, scope exclusions)
- A specialist mode signal (
webapp/api/identity/network)
CHAIN is the second half of REASON: the chain-builder looks for A→B exploit chains that elevate severity. CHAIN reads only findings.jsonl and per-hunter markdown notes; it has no HTTP access.
TEST · Strike
Three contact points confirm the catch. Re-prove every finding three times against the live target.
Implemented by the execution portion of HUNT + VERIFY (three rounds).
This is the Multi-Step Evidence contract. A finding is not eligible for SUBMIT until all three rounds agree:
| Round | Verifier | Default posture | Survives if |
|---|---|---|---|
| 1 | brutalist-verifier | "This isn't real, prove me wrong" | Re-running the PoC produces the same evidence |
| 2 | balanced-verifier | Catches false negatives the brutalist over-rejected | A finding the brutalist killed is actually exploitable |
| 3 | final-verifier | Fresh HTTP requests, fresh context, on only survivors | The bug is reproducible from scratch |
Each round writes through mantis_write_verification_round and reads through mantis_read_verification_round. No markdown is on the critical path.
LEARN · Hold
Three crystals in the grip. Stillness, not celebration.
Implemented by GRADE + REPORT + (optional) EXPLORE + fleet-intelligence write-back.
| Activity | Output | Who reads it |
|---|---|---|
| 5-axis scoring | grade.json | Report writer + orchestrator |
| SUBMIT / HOLD / SKIP verdict | grade.json.verdict | Orchestrator (drives next phase) |
| Submission-ready report | report.md | You / the triager |
| Optional patch suggestion | patch.md | The vendor's engineer |
| Optional gated email send | Gmail draft | The vendor's security contact |
The grader leads with the Evidence, Not Alerts contract: a finding earns SUBMIT only if Multi-Step Evidence is present.
How this overlays the 7-phase FSM
DISCOVER → RECON, AUTH
REASON → HUNT (planning), CHAIN
TEST → HUNT (execution), VERIFY ×3
LEARN → GRADE, REPORT, EXPLORE, fleet write-backInternally, the FSM is the truth. Externally, Mantis is the story.